|
|
 | BS Hacker is a unique hacking simulation game. You enter the underground world and play the role of a hacker, working against a system that aims to control everything. A complete hacker console and interface will create a perfect hacker environment, while the realism of the game elements will make y...
|
 | BS Hacker is a unique hacking simulation game. You enter the underground world and play the role of a hacker, working against a system that aims to control everything. A complete hacker console and interface will create a perfect hacker environment, while the realism of the game elements will make y...
|
 | Get your old Win32 apps looking like their Windows XP counterparts! XP Style Hacker is a small unique tool that instantly transforms applications that do not recognise Windows XP visual styles to be "style aware". Just select the EXE file from the program dialog and the next time you run the program...
|
 | Get your old Win32 apps looking like their Windows XP counterparts! XP Style Hacker is a small unique tool that instantly transforms applications that do not recognise Windows XP visual styles to be "style aware". Just select the EXE file from the program dialog and the next time you run the program...
|
 | Play the role of Brian Spencer, a former intelligence agent, against a complex enemy created by an artificial intelligence. From the creators of a successful hacker games series (Digital Hazard, BS Hacker, etc) Hacker Evolution is a new hacking simulation game, featuring unparalleled graphics and fe...
|
 | Play the role of Brian Spencer, a former intelligence agent, against a complex enemy created by an artificial intelligence. From the creators of a successful hacker games series (Digital Hazard, BS Hacker, etc) Hacker Evolution is a new hacking simulation game, featuring unparalleled graphics and fe...
|
 | Use your intelligence to stop another catastrophic attack over the Net. Alex D. is a programmer that works at a software company during the day, and during the night he is testing software vulnerability on companies servers. During one night he is attacking a cover up firm for a NSA operations and g...
Tags: er, decrypt, password, money, transfer, rvl, rvler, rvlgames, |
 | Using this program you can prevent the deletion of certain files/folders on a shared drive in your network. For example you've got a file you want to show to your friends. So you copy it to a shared drive in your network, and ask your friends to check it out. But some jealous freak keeps on deleting...
|
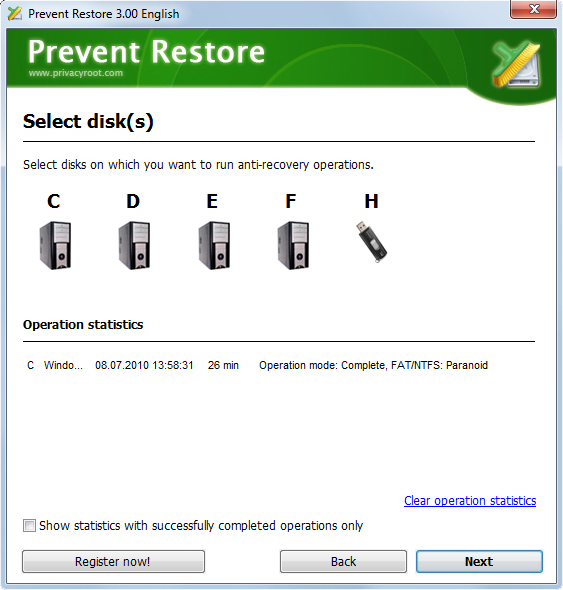
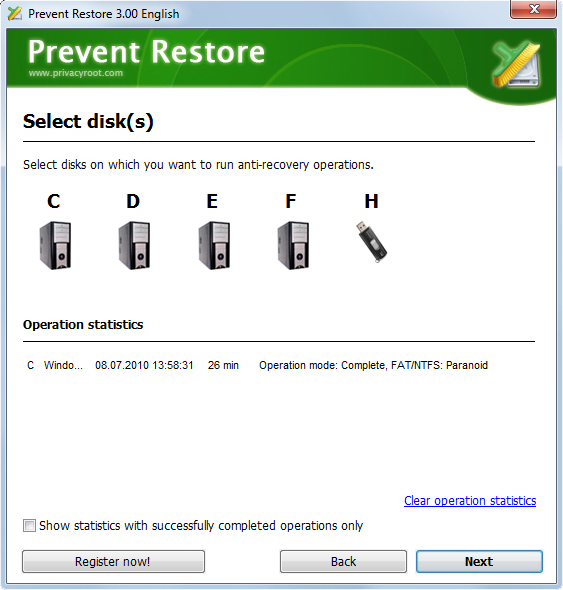 | Purpose of free "Prevent Restore" program is to make deleted files and folders unrecoverable. Its made as Wizard program and will be friendly for any computer newbie. "Prevent Restore" will overwrite all free space on your hard disks that can contain fragments of deleted files with some random data ...
|
Penguin Race - Happy Racing and Jumping Game - The Sun Classic - 아가레스트전기 친구추가(카카오톡게임친구/게임초대/친구) -
 | Advanced Anti Keylogger is powerful but easy to use anti-spy software to prohibit operation of any keyloggers currently in use or presently being developed anywhere. Once installed our anti-spy software will protect your privacy immediately and constantly. One particularly scary and dangerous featur...
|
 | Advanced Anti Spy is powerful but easy to use anti-spy software to prohibit operation of any keyloggers currently in use or presently being developed anywhere. Once installed our anti-spy software will protect your privacy immediately and constantly. It does not rely on a spyware database or require...
|
 | Desktop Lock is a computer security protection and access control software product, you can use it to lock computer to prevent people from accessing your private documents and resources. When the computer being locked by Desktop Lock, none can access your documents, browse your computer, or use prog...
|
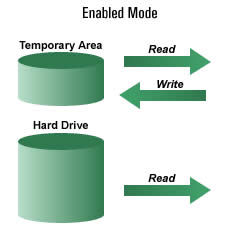
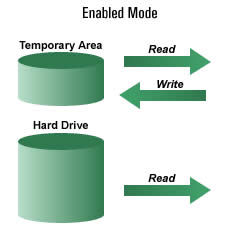 | 1. Allow users full access to their systems 2. With a simple reboot any changes to the system vanish 3. Remote administration features 4. Protection is invisible to end users 5. Easy to use and install software solution - helps reduce system maintenance. Save time and money! 6. Allows saving of file...
|
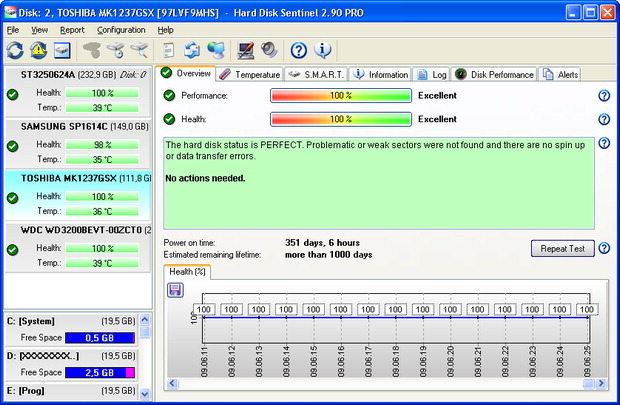
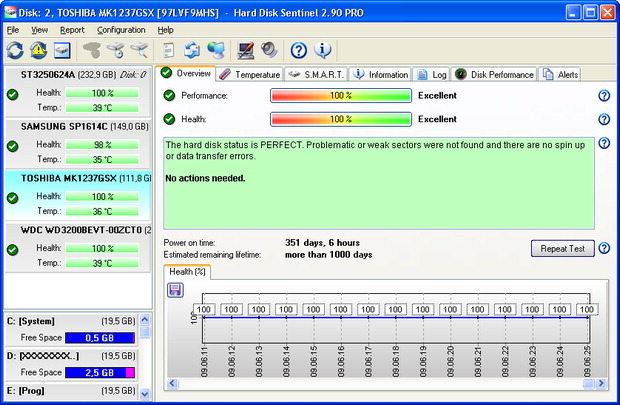 | Hard Disk Sentinel Professional offers complete data protection solution by monitoring HDDs and SSDs and provides detailed storage information, statistics, alerts and backup functions. Hard Disk Sentinel points on current or future disk problems like high temperature or degradation of disk health, w...
|
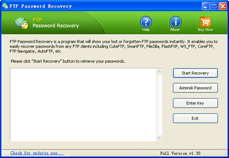
 | FTP Password Recovery is a program to recover logins and passwords for all FTP accounts stored by FTP client software. It's very easy to use and works with CuteFTP, SmartFTP, FileZilla, FlashFXP, WS_FTP, CoreFTP, FTP Control, FTP Navigator, FTP Voyager, WebDrive, SecureFX, AutoFTP, 32bit FTP, Bullet...
|
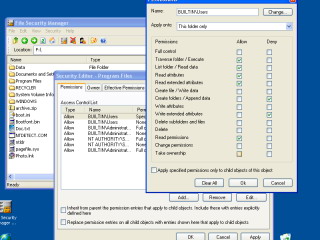
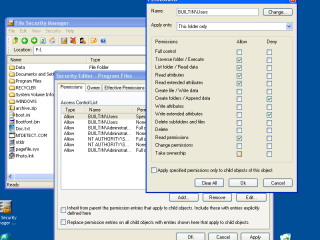
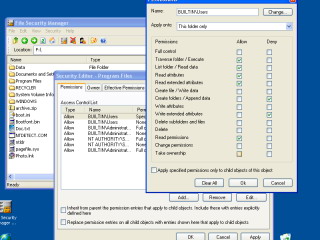 | Manage file and folder permissions (access rights) in Windows XP Home like Windows XP Professional users! As far as you know, in Windows XP Home security tab of the folder properties window can not be enabled. This program solves the problem and allows you edit advanced permissions, change owner of ...
Tags: ntfs, security, access control, windows xp, laptop, home, xp home edition, permissions, file management, file system, secure, wipe, deletion, permissions assignment, security, tab, secure, lock, prevent, user, rights, securing, remove, restrict, deny, |
 | Manage file and folder permissions (access rights) in Windows XP Home like Windows XP Professional users! As far as you know, in Windows XP Home security tab of the folder properties window can not be enabled. This program solves the problem and allows you edit advanced permissions, change owner of ...
|
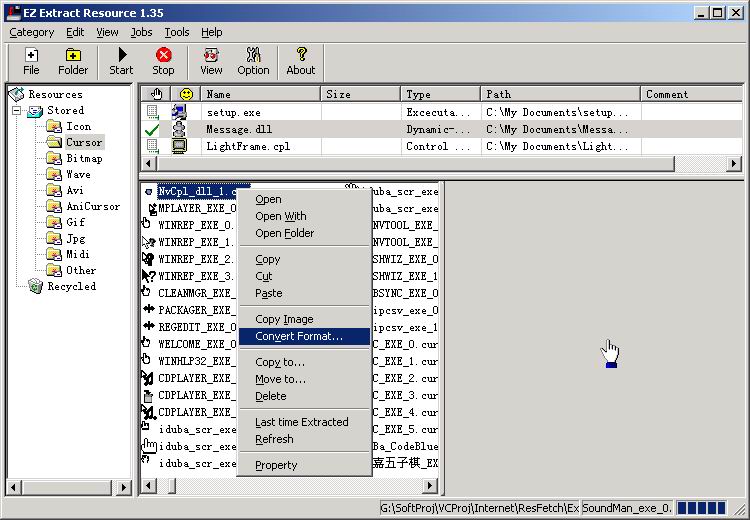
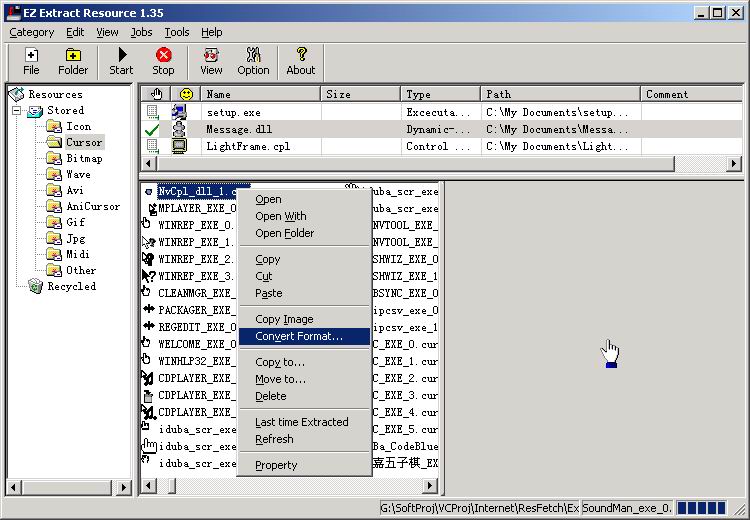 | EZ Extract Resource is a tool that can scan specified directories or single files on your computer and extract icons, bitmaps, glyphs (button images), and cursors, sounds etc from programs and DLL, OCX, etc. EZ Extract Resource save these images or videos, sounds as regular files. And can also manag...
|
 | CheckQuota is the professional monitor program for directories. It monitors directory size, sends alerts and locks write processes if a limit was exceeded. The main functions of CheckQuota are: Directory quota function:With CheckQuota it is possible to specify one or more users for your directories....
Tags: disk, quota, check, folder, directory, directories, monitor, usage, limit, size, prevent, access, write, lock, report, mail, alert, process, file, type, block, blocking, exceed, api, e-mail, windows, disk quota, directory quota, folder quota, |
 | CheckQuota is the professional monitor program for directories. It monitors directory size, sends alerts and locks write processes if a limit was exceeded. The main functions of CheckQuota are: Directory quota function:With CheckQuota it is possible to specify one or more users for your directories....
|
 | Tagg is a file utility which helps you organize your files through the use of tags. Use it to catalog your personal files as well as your media assets such as clip art,sound files or video clips. Tagg also supports plugins for integrated file previewing. The following plugins are provided: ImagePlug...
|
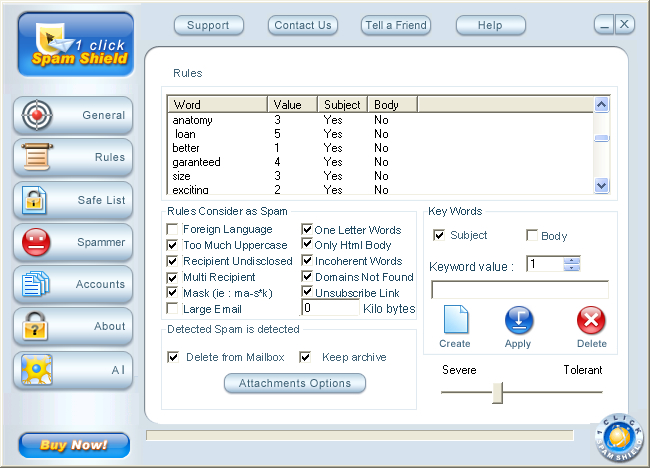
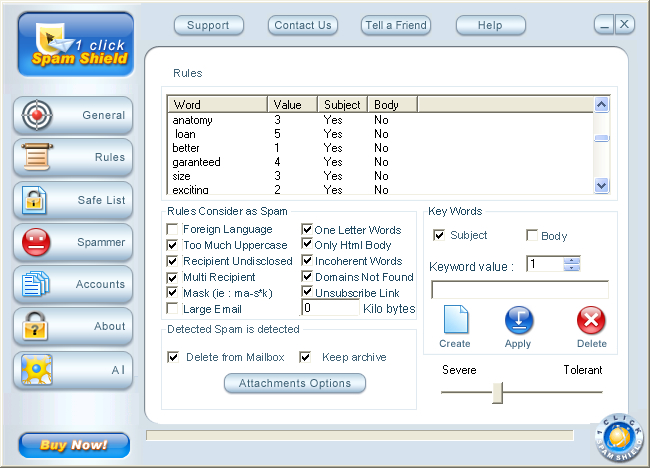 | 1 Click Spam Shield is the solution for eliminating one of the biggest threats of the mailing systems: spam. With this utility, you are receiving all your email safely and securely, all filtering being done in a transparent way, resulting in a clean Inbox with just solicited mail and no more junk. T...
Tags: stop spam, spam abuse, unsolicited email, stop spam, spam removal, spammer, security, virus security, firewalls, er protection, personal firewall, free software, anti virus, anti-virus enterprise, protect email, web junk mail, trojan horse, |
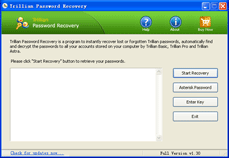
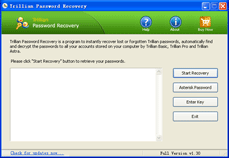 | Trillian Password Recovery instantly recovers lost or forgotten Trillian account information. It works with all versions of Trillian. Trillian is a multi-protocol instant messenger client for Microsoft Windows, so you can sign in to the Trillian messenger with many accounts such as AIM, ICQ, MSN, Ya...
|
 | a-squared Anti-Malware protects your PC from Malware-based hacker attacks. Its special capabilities in dealing with Trojans, Worms, Dialers, Adware and Spyware make it an indispensable enhancement to any protection system, whether on a private PC or a company network. The unique Malware-IDS technolo...
|
|
|