|
|
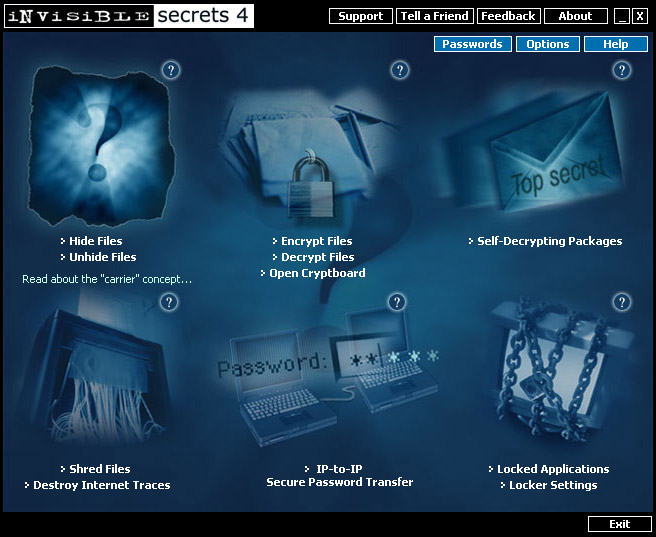
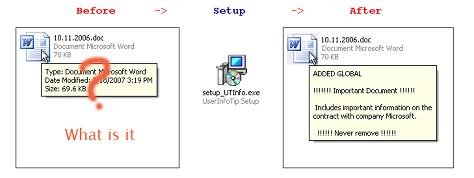
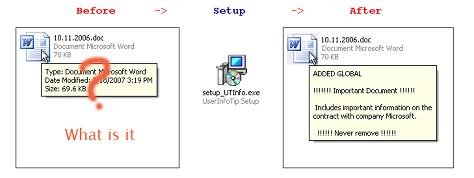
 | Invisible Secrets Encryption Software 4 not only encrypts your data and files for safe keeping or for secure transfer across the net, it also hides them in places that on the surface appear totally innocent, such as picture or sound files, or web pages. These types of files are a perfect disguise fo...
|
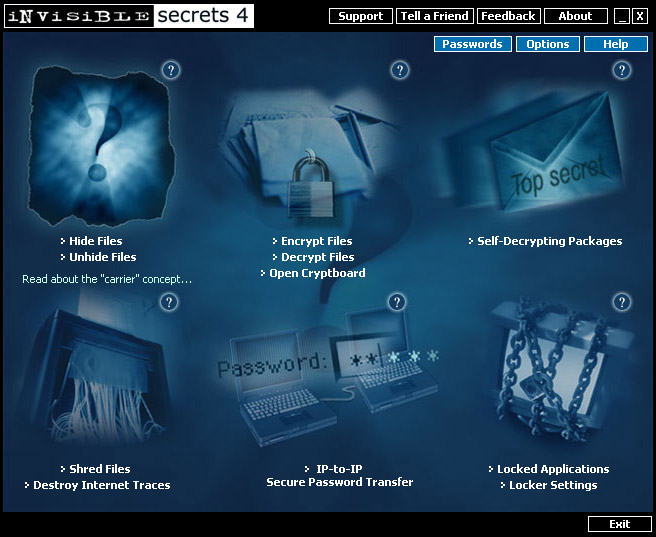 | Invisible Secrets Encryption Software 4 not only encrypts your data and files for safe keeping or for secure transfer across the net, it also hides them in places that on the surface appear totally innocent, such as picture or sound files, or web pages. These types of files are a perfect disguise fo...
|
 | The Invisible Private Folder can help you keep your files protected from kids, friends and co-workers. It allows you to add any folders to the virtual invisible private folder. It enables you to block and hide any file or folder you do not want to be accessible to others. There are two user modes: o...
|
 | Actual Invisible Keylogger is the most powerful stealth keylogger software. Actual Invisible Keylogger runs silently at the lowest level of windows capturing every keystroke typed including usernames and windows log-on passwords. Actual Invisible Keylogger can also capture active window text, text t...
|
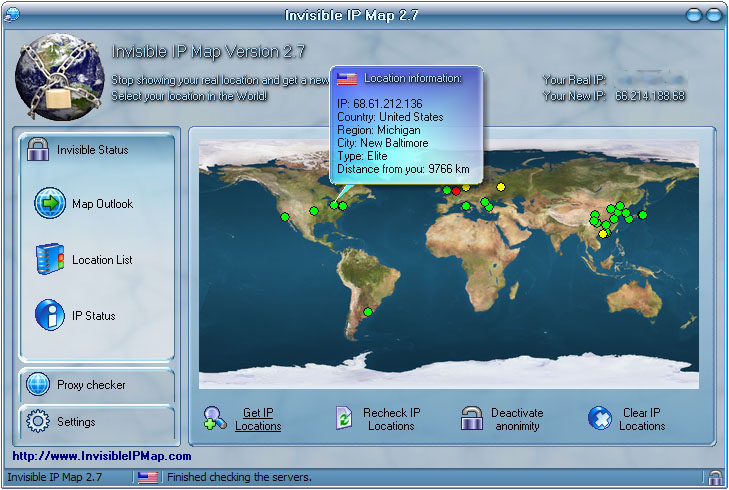
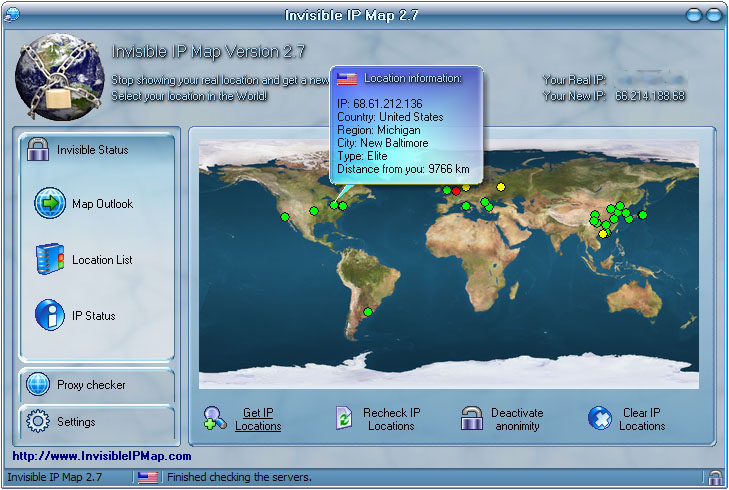 | This is a Mask IP software which is used to change your real Internet address while browsing. The software will deliver you fresh anonymous proxy servers every time you decide to click on "Get IP Locations". The main benefit of this software is that you can't be traced when browsing websites. Also i...
|
 | Stego product for Windows with a CHAOS interface and a very large hiding capacity (~100% of carrier file). Includes built-in encryption and ability to hide data within specific sub-areas of the image. Chaos uses the newest chaos logic and stream cipher. It has high speed and allows variable-length k...
|
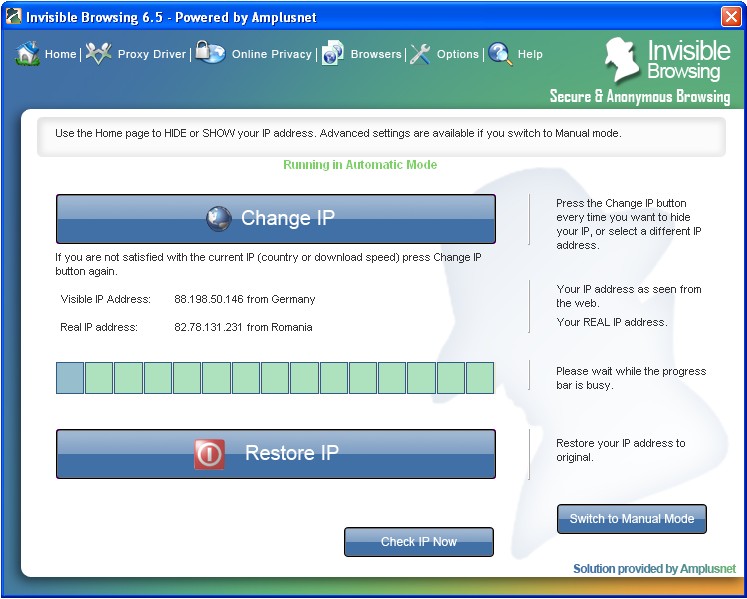
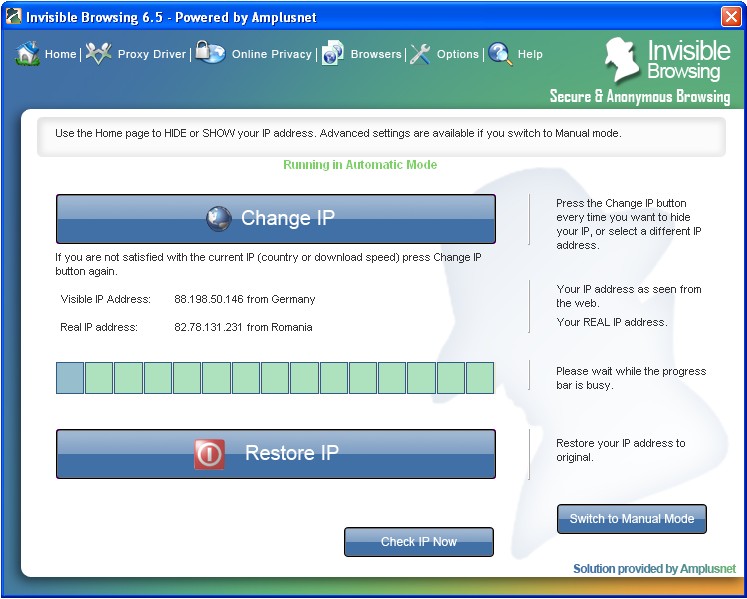 | Invisible Browsing suits both less experienced users and advanced users, through his manual or automatic mode. The manual mode allows you make all the settings, to choose the proxy and test it, while in the automatic mode all you have to do is a simple click on the button and you will surf anonymous...
Tags: amplusnet, invisible browsing - secure, anonymous, software to hide ip address, internet track eraser, online privacy, mask ip, hide ip, spoof ip address, share internet connection, proxy, pop up blocking, popup blocker, pop up stopper, popup killer, |
 | www.Featurized.com - What's hot ? Everything featured is hot ! Get Featured, Get Known. You will find everything that is hot and therefore featured on our website. Anything interesting will be announced on our website and in our newsletter. Check out our website and signup for the Featurized.com new...
|
APSC 2014 - 1tube.my - KidsWiz ABC Fruits Animal Book - Resident Evil 6 HD Wallpapers - yankii - App Smoker - UNOFFICIAL MINECRAFT BUILD MOD -
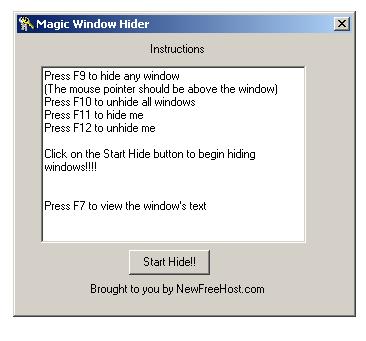
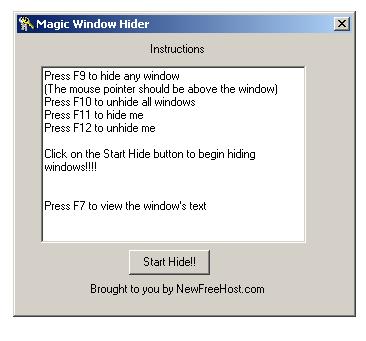 | Hide/Unhide any application/window with ease. Ever wanted to hide windows you did not want you boss/parents to see while u r working(or playing!!!),magic windows let's u hide/unhide windows with ease. Also hides itself and displays the tilte of the hidden windows by pressing F7. Just a simple progra...
|
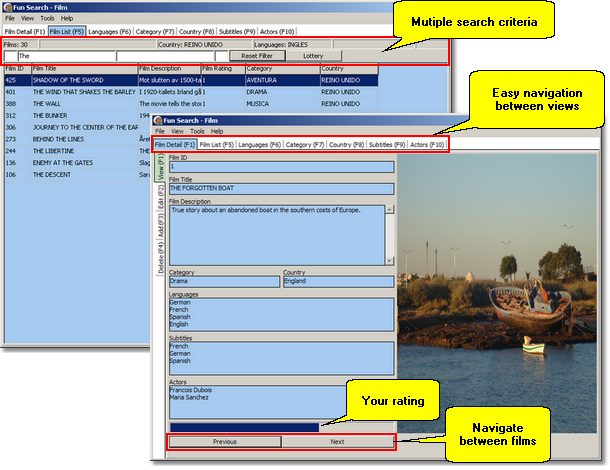
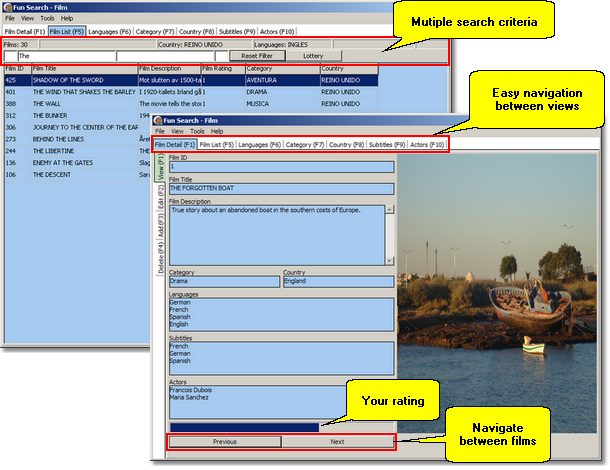 | Fun Search Film is a simple and easy-to-use database software to store and organise your personal collection of films and DVDs. The system is capable to store thousands of films entries including among other things film name, description, category and cover image. With Fun Search Film you can do all...
|
 | SafeSystem is the perfect complement to any anti-virus or anti-spyware program and allows you to prevent access to your personal and important files and folders, as well as protect and guarantee the integrity and well functioning of your system. It can make your files and folders completely invisibl...
|
 | SafeSystem is the perfect complement to any anti-virus or anti-spyware program and allows you to prevent access to your personal and important files and folders, as well as protect and guarantee the integrity and well functioning of your system. It can make your files and folders completely invisibl...
|
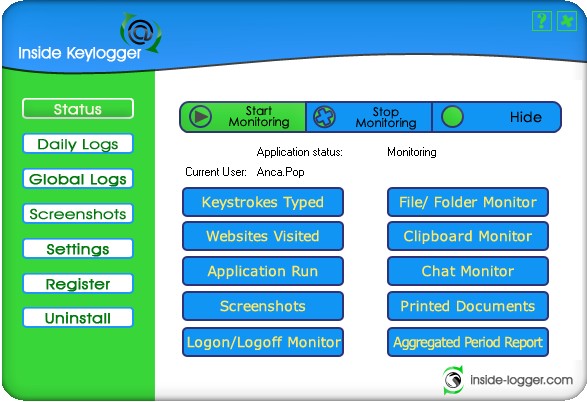
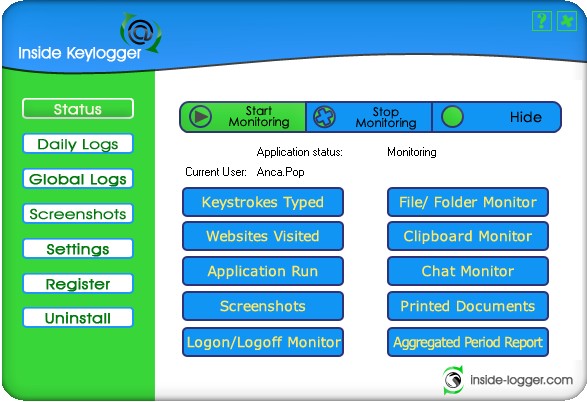 | Inside Keylogger records all activities performed on a remote computer and sends reports to a specified email address. It provides a complete image of a machine, recording everything from keystrokes, to chat conversations, printing, application monitoring, internet activity, modified files/folders, ...
|
 | I want to share with you my experience of using Keylogger King Pro. In our department, we use several methods of work-time effectiveness control. One of them, a daily report, was our best achievement so far. Yet, I was unable to precisely determine the time needed by our employees to finish certain ...
|
 | Information...priceless! Modern programs do their best to protect you from data loss. Text editors create backup copies of documents, web browsers remember login info that you enter on Web pages. Password managers help you manage your passwords, backup managers help you backup virtually everything. ...
Tags: spy software, keylogger, key logger, hardware keylogger, keystroke recorder, keystroke logger, keytrap, invisible keylogger, keyboard logger, keyboard monitor, keyboard monitoring, keycopy, keystroke recorder, keystroke recorder, |
 | You are buying a computer for your kids. You purchase tons of educational software for them so they can increase their IQs. You pay for a broadband Internet connection to allow your kids to absorb useful information. And what happens? Instead of using the computer for good, they end up playing stupi...
|
 | Anonymity Gateway masks your IP address preventing websites or ISPs from monitoring your surfing habits and your internet activity. Anonymity Gateway uses proxy servers to route your internet traffic, meaning that your internet requests will be sent to and contented by this neat server instead of th...
|
 | Folder Shield can be used to hide any folders completely and securely. Your personal documents, private photographs etc. are invisible, and hence no longer accessible, as soon as the relevant folders have been hidden with Folder Shield. Just specify all confidential folders, activate Folder Shield's...
Tags: security, secure, hide, conceal, hide folders, hide files, conceal folders, hide folder, windows security, download, restrict access, software, make folders invisible, hide directory, conceal directories, hide directories, |
 | Ultimate Keylogger is the popular all-round monitoring solution. Application monitors all activities on computer systems including applications, keyboard, passwords, clipboard, chat, email, and visited websites. To avoid tampering of the software, it features a unique file protection. Ultimate Keylo...
|
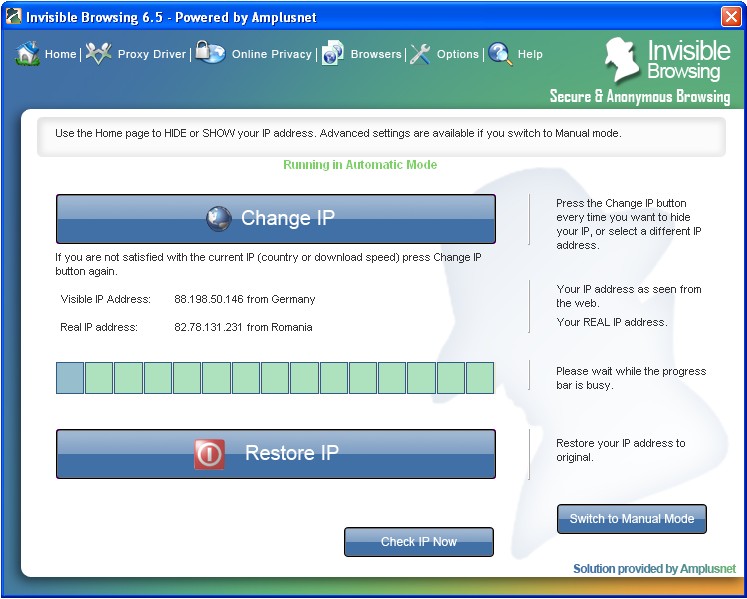 | Invisible Browsing suits both less experienced users and advanced users, through his manual or automatic mode. The manual mode allows you make all the settings, to choose the proxy and test it, while in the automatic mode all you have to do is a simple click on the button and you will surf anonymous...
|
 | Build professional banners, advertisements and other commercial animations in minutes, with an impressively short learning curve. Animation Workshop handles the elements of its animations as objects, eliminating the need to understand how animation files are structured. Animation Workshop will assem...
Tags: banner, animation, advertisement, advertising, gif, transparency, windows, shareware, alchemy, gif animation, web animation, avi, mov, quicktime, banner construction, gif compression, gif construction set, swf, mng, flash, avi, mov, www, web, html, |
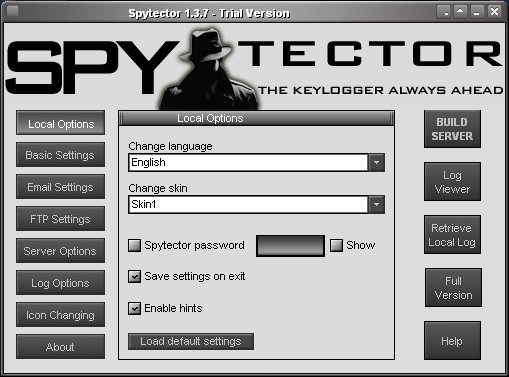
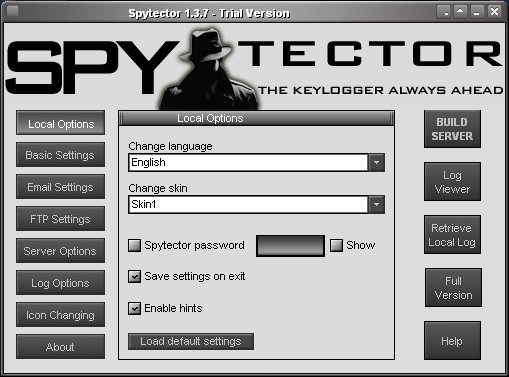 | Spytector is the ultimate invisible keylogger (spy tool) used to track all activities on a PC. Spytector is tracking all the activities of PC users (visited websites, all the keystrokes, both sides of chat conversations, opened windows etc.) and delivers the logs to you via Email or/and FTP. In the ...
|
 | ElectraSoft 32bit Web Browser runs on 32bit and 64bit computers. This Browser software program even lets you run 32-bit online audio and video player applications like YouTube, Adobe Flash Player on your 64-bit computer. 32bit Web Browser is easy to use is very fast. This web browser makes browsing ...
|
|
|